PDF] Power Consumption-based Detection of Sabotage Attacks in
Por um escritor misterioso
Descrição
This work proposes a novel approach for detecting sabotage attacks in additive Manufacturing, based on continuous monitoring of the current delivered to all actuators during the manufacturing process and detection of deviations from a provable benign process. Additive Manufacturing (AM), a.k.a. 3D Printing, is increasingly used to manufacture functional parts of safety-critical systems. AM's dependence on computerization raises the concern that the AM process can be tampered with, and a part's mechanical properties sabotaged. This can lead to the destruction of a system employing the sabotaged part, causing loss of life, financial damage, and reputation loss. To address this threat, we propose a novel approach for detecting sabotage attacks. Our approach is based on continuous monitoring of the current delivered to all actuators during the manufacturing process and detection of deviations from a provable benign process. The proposed approach has numerous advantages: (i) it is non-invasive in a time-critical process, (ii) it can be retrofitted in legacy systems, and (iii) it is airgapped from the computerized components of the AM process, preventing simultaneous compromise. Evaluation on a desktop 3D Printer detects all attacks involving a modification of X or Y motor movement, with false positives at 0%.
![PDF] Power Consumption-based Detection of Sabotage Attacks in](https://image.slidesharecdn.com/uosssimplesabotagesm-100517211219-phpapp02/85/u-oss-simple-sabotage-field-manual-1-320.jpg?cb=1667535699)
U) OSS Simple Sabotage Field Manual
![PDF] Power Consumption-based Detection of Sabotage Attacks in](https://wires.onlinelibrary.wiley.com/cms/asset/f68fce80-1c81-4dce-95c9-6543e2855f8d/widm1211-toc-0001-m.jpg)
Enterprise data breach: causes, challenges, prevention, and future directions - Cheng - 2017 - WIREs Data Mining and Knowledge Discovery - Wiley Online Library
![PDF] Power Consumption-based Detection of Sabotage Attacks in](https://ietresearch.onlinelibrary.wiley.com/cms/asset/3da0c48b-c5ee-42dd-9bf0-975b59c48459/gtd212766-fig-0002-m.jpg)
A novel cyber‐attack modelling and detection in overcurrent protection relays based on wavelet signature analysis - Yousefi kia - 2023 - IET Generation, Transmission & Distribution - Wiley Online Library
![PDF] Power Consumption-based Detection of Sabotage Attacks in](https://media.kasperskycontenthub.com/wp-content/uploads/sites/43/2022/12/12092633/KSB_2022_Story_of_the_year_01.png)
Reassessing cyberwarfare. Lessons learned in 2022
![PDF] Power Consumption-based Detection of Sabotage Attacks in](https://ars.els-cdn.com/content/image/1-s2.0-S0306261922002707-ga1.jpg)
Incentive edge-based federated learning for false data injection attack detection on power grid state estimation: A novel mechanism design approach - ScienceDirect
![PDF] Power Consumption-based Detection of Sabotage Attacks in](https://ars.els-cdn.com/content/image/1-s2.0-S0278612522000632-gr3.jpg)
Physics-based detection of cyber-attacks in manufacturing systems: A machining case study - ScienceDirect
![PDF] Power Consumption-based Detection of Sabotage Attacks in](https://www.mdpi.com/jcp/jcp-02-00027/article_deploy/html/images/jcp-02-00027-g001.png)
JCP, Free Full-Text
![PDF] Power Consumption-based Detection of Sabotage Attacks in](https://www.frontiersin.org/files/Articles/850056/fsens-03-850056-HTML/image_m/fsens-03-850056-g006.jpg)
Frontiers Hardware Security in Sensor and its Networks
![PDF] Power Consumption-based Detection of Sabotage Attacks in](https://pubs.acs.org/cms/10.1021/acsnano.1c10635/asset/images/acsnano.1c10635.social.jpeg_v03)
Nanotechnology Tools Enabling Biological Discovery
![PDF] Power Consumption-based Detection of Sabotage Attacks in](https://ietresearch.onlinelibrary.wiley.com/cms/asset/ccc72dff-7383-4e3c-9060-7a21c5f1a1da/cps212064-fig-0003-m.jpg)
A new stable scheme against false data injection attacks in distributed control microgrid - Tahani - IET Cyber-Physical Systems: Theory & Applications - Wiley Online Library
![PDF] Power Consumption-based Detection of Sabotage Attacks in](https://media.springernature.com/m685/springer-static/image/art%3A10.1038%2Fs41598-023-40273-8/MediaObjects/41598_2023_40273_Fig9_HTML.png)
A cluster-based trusted routing method using fire hawk optimizer (FHO) in wireless sensor networks (WSNs)
![PDF] Power Consumption-based Detection of Sabotage Attacks in](https://csis-website-prod.s3.amazonaws.com/s3fs-public/2023-07/230713_OnFuture_War_Banner.jpg?VersionId=VK7QDjXJHkXr6wDgQRQon.lOwdTycuYE)
Cyber Operations during the Russo-Ukrainian War
![PDF] Power Consumption-based Detection of Sabotage Attacks in](https://www.researchgate.net/profile/Mark-Yampolskiy/publication/319524597/figure/fig3/AS:535794354196480@1504754736804/Standard-deviation-of-X-traces-over-time_Q320.jpg)
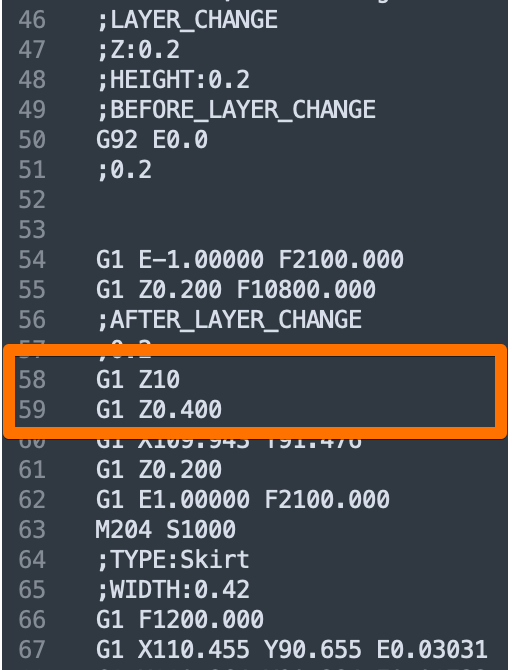
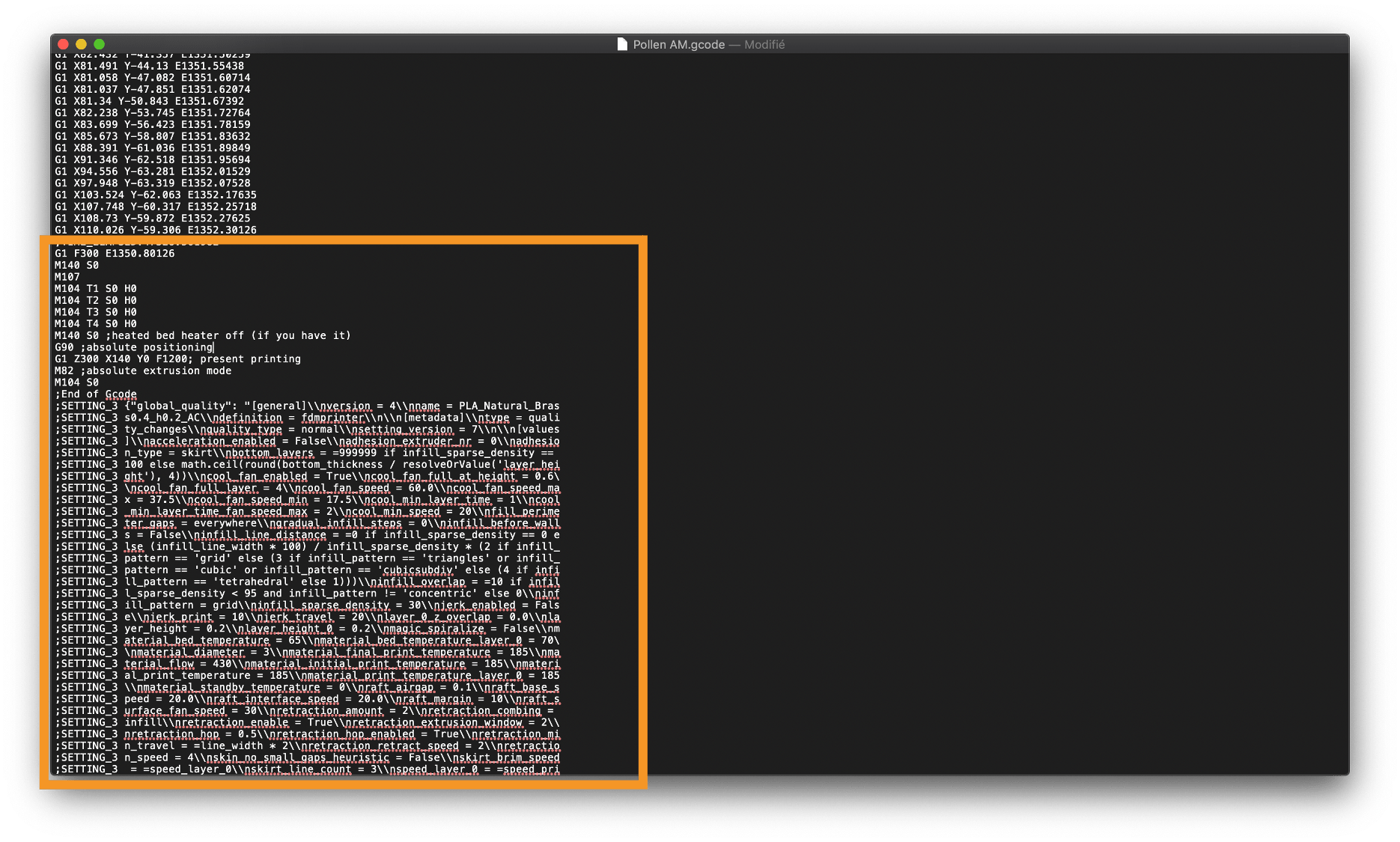
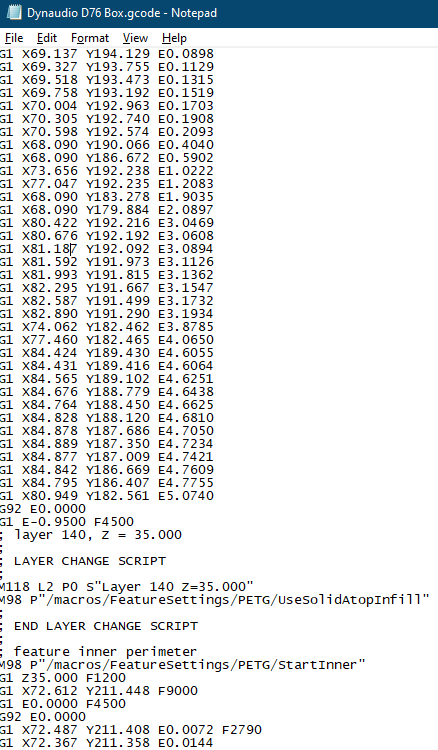
PDF) Power Consumption-based Detection of Sabotage Attacks in Additive Manufacturing
![PDF] Power Consumption-based Detection of Sabotage Attacks in](https://d3i71xaburhd42.cloudfront.net/d81c8d2816032b4abc1798383f88d5a376d17a75/8-Figure2-1.png)
PDF] Power Consumption-based Detection of Sabotage Attacks in Additive Manufacturing
![PDF] Power Consumption-based Detection of Sabotage Attacks in](https://d3i71xaburhd42.cloudfront.net/d81c8d2816032b4abc1798383f88d5a376d17a75/9-Table1-1.png)
PDF] Power Consumption-based Detection of Sabotage Attacks in Additive Manufacturing
de
por adulto (o preço varia de acordo com o tamanho do grupo)