Reverse Engineering Nike Run Club Android App Using Frida - Yasoob Khalid
Por um escritor misterioso
Descrição
Hi everyone! 👋 If you have been following my blog then you might have already read the article on reverse engineering an Android app by writing custom smali code. I am still very much a reverse engineering beginner so after that article, I got to learn about Frida. I was told that Frida is much faster and a lot easier for scenarios where I want to snoop on functions. Well, I am glad to report that all the suggestions were absolutely correct.

Jaroslav Nahorny (@JaroslavNahorny) / X
Reverse Engineering Nike Run Club Android App Using Frida - Yasoob Khalid
GitHub - iamsarvagyaa/AndroidSecNotes: An actively maintained, Self curated notes related to android application security for security professionals, bugbounty hunters, pentesters, reverse engineer, and redteamers.
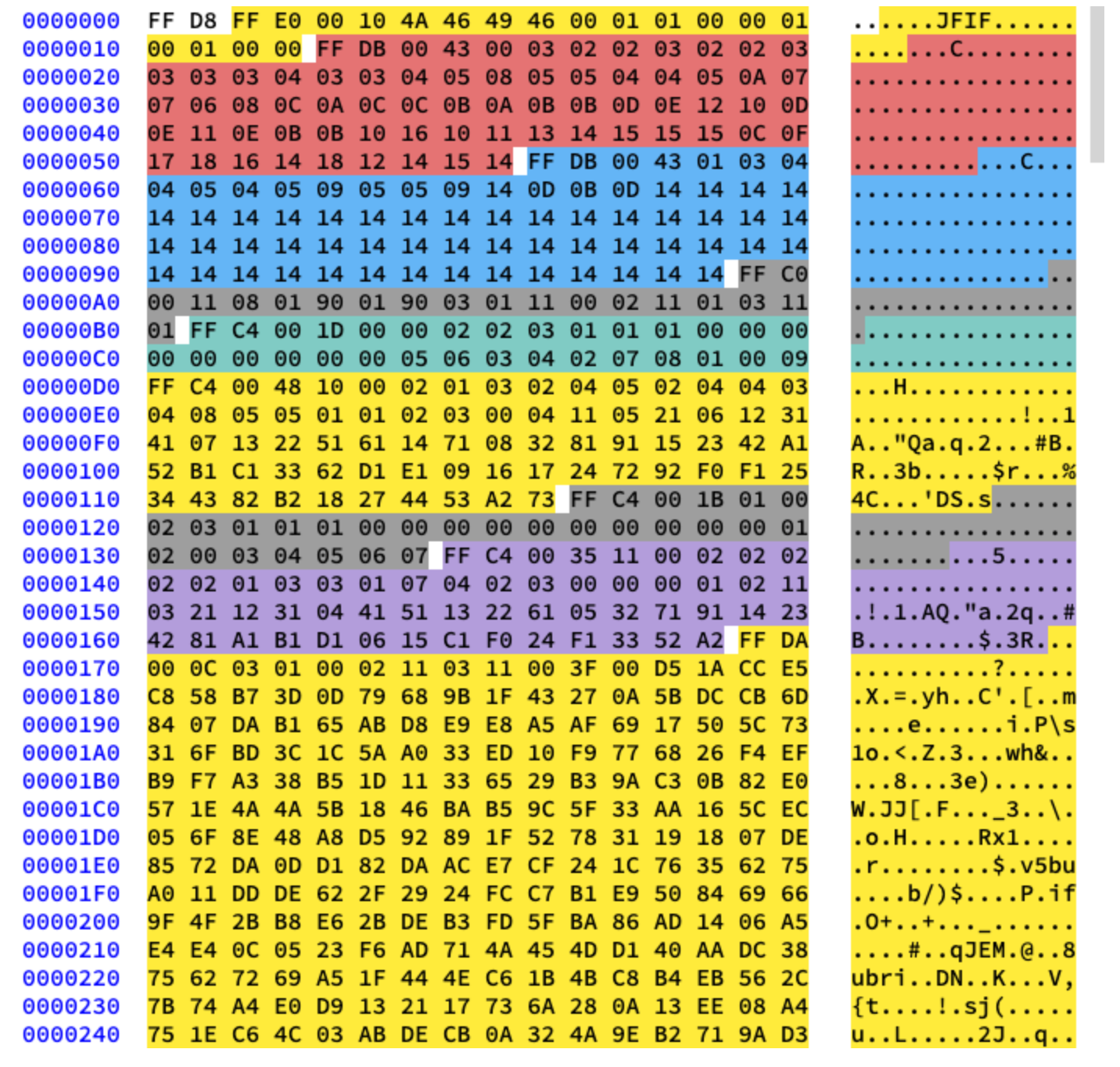
Understanding and Decoding a JPEG Image using Python - Yasoob Khalid
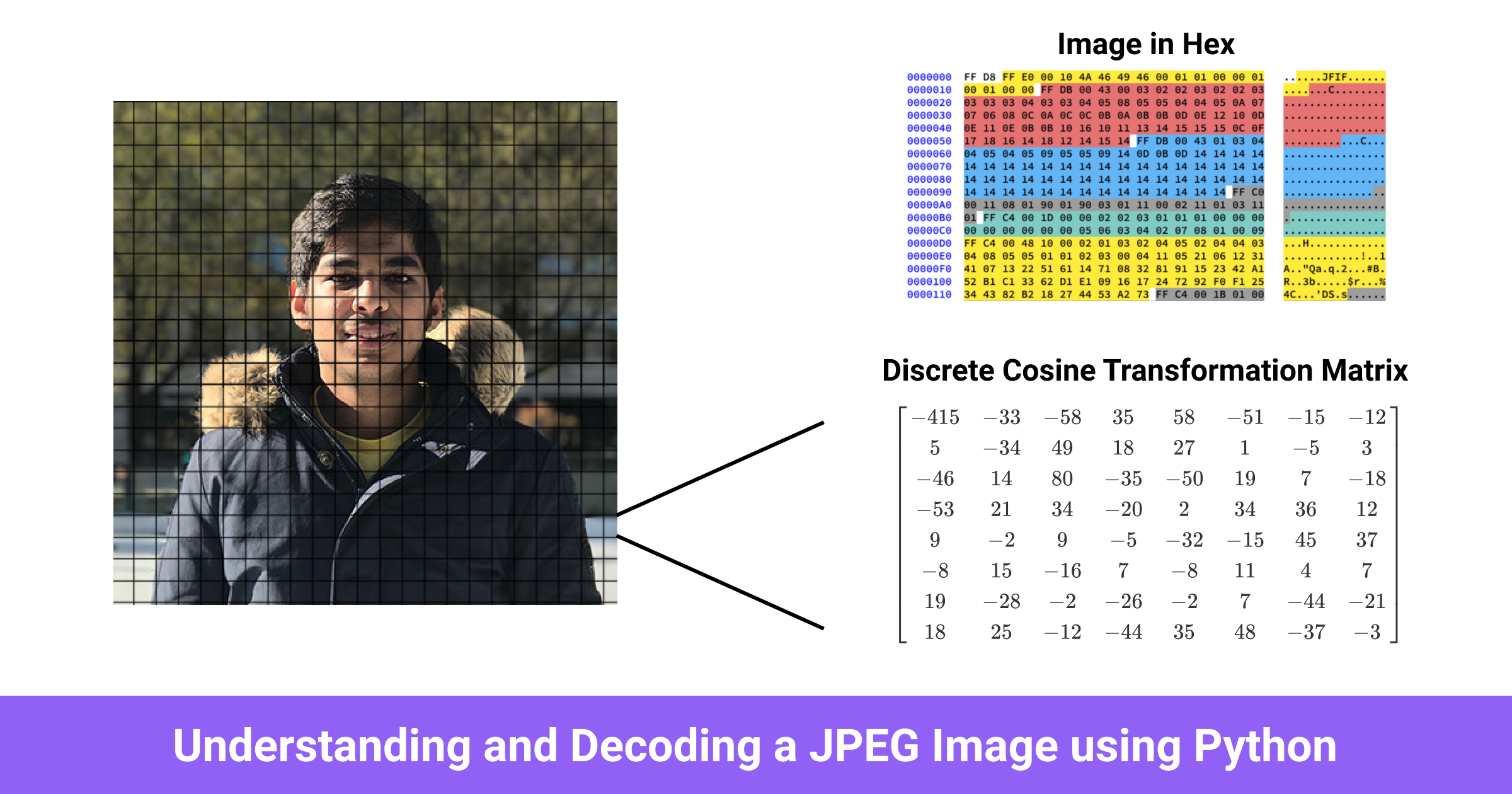
Understanding and Decoding a JPEG Image using Python - Yasoob Khalid

Python Tips
Jaroslav Nahorny (@JaroslavNahorny) / X
Understanding and Decoding a JPEG Image using Python - Yasoob Khalid
yasoob (M.Yasoob Ullah Khalid ☺) · GitHub
Jaroslav Nahorny (@JaroslavNahorny) / X
Rahul Barhate 🎩 🐇 (@d4rw1nk5) / X

GitHub - yasoob/nrc-exporter: Download your runs data from Nike Run Club and convert it to GPX format that can be imported in other running apps.

Let's Reverse Engineer an Android App! - Yasoob Khalid
de
por adulto (o preço varia de acordo com o tamanho do grupo)